Welcome to the wonderful world of canonicals and HTTPS, where there are endless bounds of confusion and needless complexity, which is why so many people can’t seem to get it working properly.
This post assumes your DNS is setup properly with your site.com A record pointing to the IP of your server, and the www.site.com CNAME pointing to your A record. It also assumes you have HTTPS working on your IIS server and that you have already bound your issued certificate to your site. You might already be forcing redirects to HTTPS, which is great, but in this post I’ll show you how to incorporate an SEO friendly aspect to the redirection, and possibly a few other things you might not be aware of.
Canonicals & Considerations
When we talk about canonicals, we talk about the way we intend our site to be consistently viewed, or referred to, across the web. In other words, this generally means choosing to refer to your site with www or without www and consistently sticking to it. Many modern sites will use the non www version, which is my recommendation because the www is already implied when we’re talking about websites and doesn’t read as cleanly. It’s just simpler.
Why would a company use www.site.com, then? It could be personal preference, but in some cases on companies’ internal networks, often times the site.com version of their domain will be set up to point to internal software such as Microsoft Active Directory, or whatever else their setup may require. The point is, when choosing your canonical, it’s probably best to go with the non www unless your internal networks would not allow for that.
Secure Canonicals
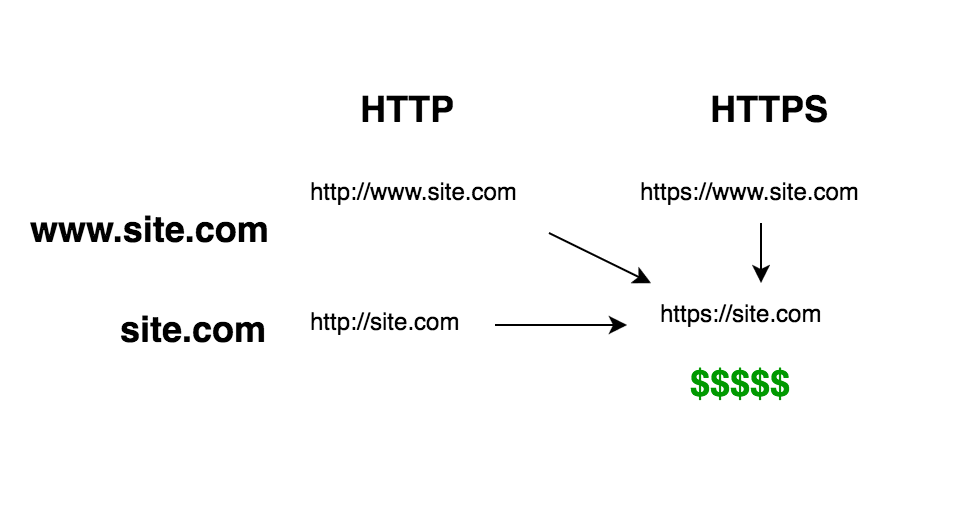
When we talk about secure canonicals, we’re talking about ensuring that anyone who navigates to your site gets redirected to a secure version of the site (https://site.com). When you combine the two, you want to ensure site visitors are redirected as follows:
The Web.config File
In order to perform this redirect, we want to use the IIS Module Rewrite functionality. First you’ll want to actually download it. If you modify your Web.config with the code below before the software is actually downloaded, the config will be considered invalid and it will break your site… So make sure you install the module on your upstream environments before deploying these config changes.
<rewrite>
<rules>
<rule name="Redirect to Secure Canonical" stopProcessing="true">
<match url="(.*)" />
<conditions logicalGrouping="MatchAny">
<add input="{HTTPS}" pattern="off" />
<add input="{HTTP_HOST}" pattern="^(www\.)(.*)$" />
</conditions>
<action type="Redirect" url="https://site.com/{R:0}" redirectType="Permanent" />
</rule>
</rules>
</rewrite>
In plain English, this rule will detect when a user has navigated to your site with either no HTTPS or with a preceding www. (assuming your site’s canonical is non www). It will then redirect the user to https://site.com while preserving query string values and returning a 301 permanent redirect response. Google recommends performing 301 redirects for this type of stuff, so we’d best listen to that advice.
Of course, this setup has limitations, which some of you may be able to spot just by looking at it. For example, this rule does NOT allow for unsecured subdomains (other than www which we swiftly slap down). If a user navigates to a subdomain via HTTP (http://subdomain.site.com), they will be redirected away from that subdomain completely (https://site.com). So just be sure that you're always connecting via HTTPS if you do have subdomains being routed through this web config.
Closing the Loop
Now that your site redirects properly and returns all of the proper error codes, you want to make sure to tell Google what your site canonical actually is. Go into Google Search Console and specify it, and may great fortunes come your way!
